RA Operations Guide
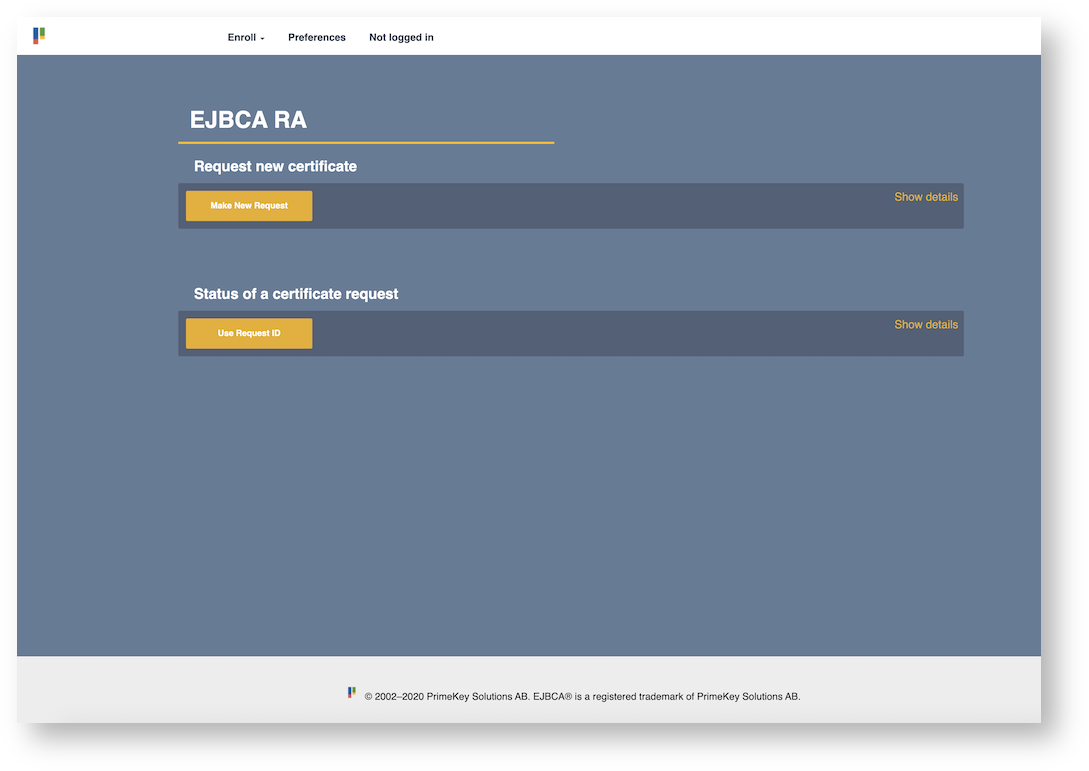
This RA Operations Guide covers EJBCA RA Management tasks and describes the EJBCA menu sections and the functions you can perform in the EJBCA RA GUI.
For information on RA concepts, see EJBCA RA Concept Guide.
Overview
The EJBCA RA UI is the portal for all end entity related operations, from enrolling certificates to administrating access for other RA administrators. The RA can either exist locally on the same instance as the CA, or be proxied to the CA via peers.
The RA can be configured to both use certificate authentication or to allow for public access. In either case, the menu items described on this page and its sub-pages will only appear in accordance to the rights set up for that user. Additionally, both the user and the peer connector itself (if using) have their access rights limited to only permitted CAs and role namespaces.
Access Rules for the RA
Authorization on the RA is fed from the configuration from the CA. To find out how to set up access rules for your RA Administrators, see RA Administrator Access Rules.
Enrolling Certificates, Creating Key Stores and Retrieving Generated Certificates
The heart of any RA is the ability to enroll for certificates and key stores. The EJBCA RA allows for both having the server generate key stores or simply sign a supplied CSR, and can also be used to pre-configure end entities for the end user to enroll against at a later date. For more information, see Creating Certificates on the RA.
Certificate and End Entity Lifecycle Management
Managing certificates is an essential day-to-day task of RA administration. The EJBCA provides a full interface for searching among certificates and end entities in order to find certificates needing renewal, or responding from requests from users to suspend and revoke certificates. For more information, see Certificate and End Entity Lifecycle Management.
Manage Requests
EJBCA's powerful approvals mechanism is naturally used in the RA as well, though it's limited to enrollment, renewal and revocation operations. The EJBCA RA provides an interface to manage approvals, view other pending approval requests and audit past operations. For more information, see Managing Requests in the RA UI.
CA Certificates and CRLs
The CA Certificates and CRLs screen allows downloading CA certificates and CRLs for CAs that you have access to.
The CAs you can access are listed in a table displaying the following:
|
Column |
Description |
|
Certificate Authority |
Name of Certificate Authority. |
|
CRL |
|
|
Certificate |
|
|
Certificate chain |
Downloads a certificate chain for a sub CA, the sub CA certificate(s) and root CA certificate:
|
|
Browser import |
Downloads the CA certificate with headers to trigger a browser import. |
Download CA Certificate Fingerprint Sheet
To download a YAML text document with the CA Certificate fingerprints of all CAs you have access to, click Download Fingerprints. This is useful during a key ceremony and eliminates the need for downloading CA certificates and computing the fingerprints manually using a third-party tool such as OpenSSL. The fingerprint is computed using SHA-256.
Download CA Certificate Bundle
To download a compressed zip file containing the CA certificates of all CAs you have access to, click Download Certificate Bundle. The certificates in the bundle are provided in binary format (DER).
Role Management
In order to allow for Managed PKI setups using the EJBCA RA, the RA makes full use of access rights and role namespaces. This allows an RA administrator with sufficient access rights to create duplicate or further constrained RA administrators within the same namespace in order to handle local user administration without needing to interact with the CA. For more information, see Managing Roles and Access Rules from the RA.
Workflows
Setting up the RA UI for Public Access
You can to set up the RA UI to allow unauthenticated users to enroll. With some minor configuration and access to port 8442, users can do so easily.
For information on how to set up the RA UI for public access, see:
Enabling Key Recovery
To perform key recovery for a user, key recovery has to be enabled in EJBCA System Configuration. To activate key recovery:
In the CA UI on the CA, go to System Configuration.
On the Basic Configuration tab, activate Enable Key Recovery.
Additionally, the end entity profile used to create the end entity requires key recovery to be enabled.
Under RA Functions, select End Entity Profiles.
Edit the End Entity Profile and select use for Key Recoverable.
Using Local Key Generation
Local key generation is used when the key recovery data (encrypted key pair) is to be stored on an external RA rather than the CA. For more information, see Key Recovery.
To activate local key generation, do the following.
In the CA UI on the RA, go to System Configuration.
On the tab Basic Configuration, for Enable Key Recovery, select Activate [x] and Force Local Key Generation [x].
Select a crypto token for encryption of the key pairs (the crypto token must be created and activated before this step).
Select a crypto token key.
Customizing the RA's Appearance
The RA's stylesheets can easily be customized and provided with a custom logo to suit your RA needs.
→ To find out how, see Customizing the RA Appearance.