EJBCA 7.7.0 Release Notes
JULY 2021
The PrimeKey EJBCA team is pleased to announce the release of EJBCA 7.7.0.
Running hot on the heals of EJBCA 7.6.0, this feature release is our final push towards full Microsoft Windows compatibility before the summer. With this release, we're aiming to be able to offer a fully holistic solution to any Microsoft based enterprise looking to power their PKI with the easiest, fastest, and most powerful solution available.
Deployment options include EJBCA Hardware Appliance, EJBCA Software Appliance, and EJBCA Cloud.
Highlights
Microsoft Windows Compatible CA Key Updates
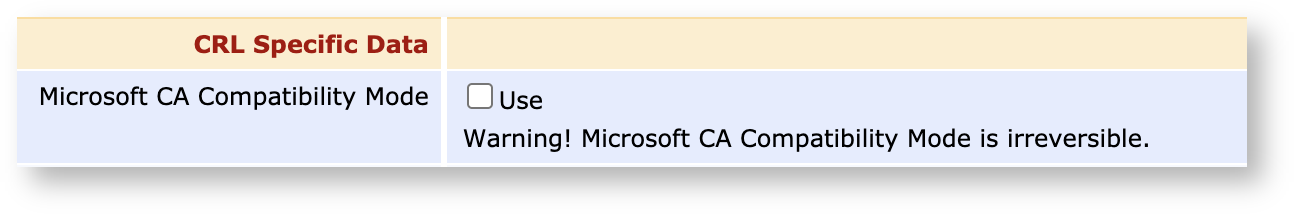
Due to some differences in how Microsoft Windows handles CRLs, we've introduced a Microsoft Compatibility mode that changes the CA's behavior when the CA is rekeyed. The commonly expected behavior when a CA is rekeyed, is that all future CRLs and OCSP responder certificates are signed by the new key pair after the rollover. Instead, Microsoft environments expect each generation of CA key pairs to continue signing CRLs for those certificates which were issued by that particular key pair. Likewise, OCSP responses are expected to be continued to be signed with an OCSP responder certificate signed by the original key pair.
The end result of Microsoft Compatibility mode is that:
The CA will produce as many CRLs as there are generations of CA keys.
OCSP responses will have different signing keys, depending on which generation of CA keys signed the relevant certificate.
Microsoft Compatibility mode comes with some caveats:
It's not possible to switch between the two modes, so Microsoft Compatibility Mode must be enabled upon CA creation if required.
Microsoft Compatibility Mode is mutually exclusive with the use of Partitioned CRLs.
For more information about EJBCA's Microsoft Compatibility mode, see Microsoft Compatible CA Key Updates.
Approvals in ACME Workflow
Upon popular demand, we have implemented Approvals for the ACME workflow. Configuring Approvals for a CA or Certificate Profiles and enrolling over ACME will now trigger an approval event for the account and subsequent end entity creation. For more information, see ACME.
Azure Blob CRL Publisher
To further increase compatibility with the Microsoft space, we have introduced a CRL publisher to Azure Blob. For more information, see Azure Blob Storage Publisher.
Announcements
Sunset of JDK8 support
With JDK8 seeing the end of its official support window from Oracle, we will towards the end of this year sunset support for JDK8 ourselves to be able to take advantage of the many features in JDK11 and later. We want to recommend all customers to upgrade their JDKs to JDK11. With the coming release of JDK17 as the next LTS release from Oracle, we will be implementing full support towards the autumn.
Upgrade Information
Review the EJBCA 7.7.0 Upgrade Notes for important information about this release. For upgrade instructions and information on upgrade paths, see Upgrading EJBCA.
EJBCA 7.7.0 is included in EJBCA Hardware Appliance 3.9.0 and EJBCA Cloud 2.8.0 and can be deployed as EJBCA Software Appliance.
Change Log: Resolved Issues
For full details of fixed bugs and implemented features in EJBCA 7.7.0, refer to our JIRA Issue Tracker.
Issues Resolved in 7.7.0
Released July 2021
New Features
ECA-3085 - Option to start audit log verification from a specified sequence number
ECA-10074 - Azure CRL Publisher
ECA-10180 - ACME Name Generation Scheme
Improvements
ECA-9797 - Documentation is missing for "extension_data" field in REST calls
ECA-9863 - SCEP: add option to include CA chain in the GetCACert call (update for RFC8894)
ECA-10050 - GUI option for Microsoft conformant CA creation
ECA-10051 - OCSP Responder support for multiple signer keys
ECA-10080 - Make ms conformant setting irreversible in other end points
ECA-10081 - Improve DynamicUiProperty field validation user mesages
ECA-10084 - UI: Hide "Partition CRL Settings" when "MS Key Updates" is enabled.
ECA-10085 - CA signKey must correspond to partition.
ECA-10086 - Suspend previous CRL partition with CA key re-keying.
ECA-10087 - Enforce Partition CRLs with MS CA Key Updates
ECA-10091 - Add approvals for ACME account management
ECA-10140 - Enforce CRL Distribution Point in Edit CA page if MS CA Compatibilty mode is selected
ECA-10152 - Enforce Use of Authority Key ID
ECA-10153 - Generating Default CRL Dist. Point should use partition suffix
Bug Fixes
ECA-9805 - Enrollment code not shown in RA web when using key recovery
ECA-10138 - Single Active Certificate Constraint sets revocation date to 1970
ECA-10166 - IntuneRevocationWorker is missing setting for AUTH_AUTHORITY in 7.7
ECA-10167 - CA certificate CDP not updated on MS CA re-keying
ECA-10174 - SCEP Issuance has incorrect log message
ECA-10194 - Azure CRL Publisher Not Publishing CRLs via peer
ECA-10197 - CRL Publisher label wrong
ECA-10198 - Azure CRL Publisher fails unless password entered